.
.
.
Related Links
Help us Choose The Next Password Manager to Review - Win a free eBook
RoboForm Password Manager Review
KeePass Password Manager Review
LastPass Password Manager Review - Page 2
One Master Password
You create one master password to unlock all your other passwords. All encryption and decryption occurs on your local computer. Lastpass does not keep your master password. They only keep a double encrypted copy of your data. Not even Lastpass employees can view your data or master password.
Safety
Lastpass uses the same encryption used by the US Government to encrypt your data. Lastpass does not keep your master password. It is not stored anywhere unless you store it yourself. Your password is applied against the encrypted local database. If the correct password is entered, it will decrypt and work. If the wrong password is entered, decryption will fail, and it will not work.
It’s impossible to ask someone to reset or email your password. Because they don’t keep your password, if you forget it the only option is to start over resetting passwords. You could also pay someone to attempt a brute force attack against your lastpass database, but unless you have a weak password, it will not be feasible to try this.
Security Options
Lastpass lets you determine many security settings, such as:
-
Logoff behavior such as after browser close and after idle.
-
Multi-Factor Authentication
-
Clear clipboard after use
-
Auto logout timeout
Automatic Form Filling
If you install the lastpass browser plugin, lastpass can fill forms for you. This is most commonly used for user name and passwords, but can be configured to fill other form fields also.
One Click Login
When you first visit a site and login with the lastpass plug-in running, you will be prompted to choose how last pass will handle future logins.
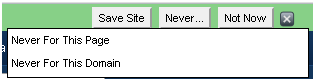
Using password managers for high risk sites is not recommended, and saying “Never for this domain”, is a good way to eliminate bothersome prompts.
Encrypted Data
Your passwords and site information is kept in the “Lastpass Vault”. This is really a file kept on your computer. The file is encrypted until you login to lastpass, where it is decrypted in memory.
Last pass uses a local “salt” before encrypting data. This means that they intermingle the plain text password with other text before encrypting, which makes it much harder to decode using methods known as rainbow tables. See What are hashes and rainbow tables
After encrypting the data locally, data is sent to lastpass servers and salted a second time before being encrypted a second time. This means that even if a rogue employee decrypts the server side data, they still just have encrypted data.
Page 1 Page 2 Page 3 Page 4 Page 5 Page 6 Page 7 Comments


|
Learn to Make Strong Memorable Passwords Today |

|
| ISBN: 978-0615456850 |
.
|
|
||
|
Home | Live CD Listing | Password Worksheet | Third Party Ratings | Purchase | Errata | Contact | News | News Archive | Legal Copyright © 2011, Sustainable Alternatives, LLC | Ligonier, PA 15658 | 724-238-9560 | All Rights Reserved. |

|
|
 |
.

