.
.
.
Lastpass Adds Windows Phone 7 App Features - 2011-12-01

Lastpass just added a security improvement feature to their Windows Phone 7 app. Users can now enable a "pin code prompt". Enabling this requires a pin after switching to another app and returning to lastpass.
All previous lastpass security remains unchanged. According to the lastpass blog: You can enable the pin code prompt in your app settings so that when multitasking back to the LastPass app, you're prompted to enter your 4-digit code. This provides an extra layer of security that's more manageable on your Windows Phone 7, since you won't have to re-enter your master password each time you reopen the app.
To enable the pin code prompt, login to the LastPass app to view your LastPass vault. Tap the ellipses (three dots) at the bottom of the screen to expand the menu options. Tap the "set pin code" option, and enter a 4-digit pin code. The next time you multitask away from and back to the LastPass app, you'll enter this pin code to regain access.
They also report that if you've enabled Google Authentication and are using it to login to the LastPass mobile app, they've improved support for switching apps when entering the Google Auth login code.
Print Friendly Single Article:Lastpass Adds Windows Phone 7 App Features
UN Hack Exposes More Weak Passwords - 2011-11-30
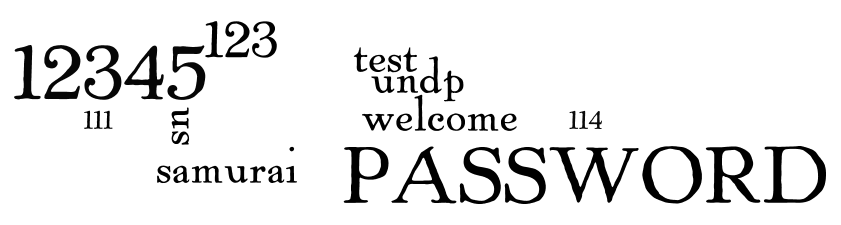
Credit word cloud to worldle.net
On Monday, the hactivist group TeaMpoiSon posted 857 usernames and passwords for members of the United Nations Development Programme (UNDP), Organisation for Economic Co-operation and Development (OECD), UNICEF, World Health Organisation (WHO) and other groups.
The top ten passwords used were:
Note: This small list of 857 usernames, email and passwords was so small several passwords hit the top ten that were probably from users with multiple accounts or admins. We've removed these from the list.
12345 PASSWORD 123 samurai sn test undp welcome 111 114
We checked both pwnedlist and shouldichangemypassword.com this morning and neither found emails on this list. We notified both sites of the list so they can load them.
Update
Eweek Europe is reporting:
UNDP spokeswoman, Sausan Ghosheh, told the BBC that the hacked server, which goes back to 2007, contained old data and no active passwords. “The UNDP found [the] compromised server and took it offline. Please note that UNDP.org was not compromised.” Reference: eWeek Europe. The eWeek article also quotes a US security expert, whom we agree with. This list exposes email addresses and passwords. Most people admit to reusing passwords at many sites.
Print Friendly Single Article:UN Hack Exposes More Weak Passwords
25 Worst Passwords of 2011 - 2011-11-18
According to PCWorld, a recent survey from SplashData compiled the 25 worst passwords of 2011. This was determined by analysis of publicly disclosed breach data.
- password
- 123456
- 12345678
- qwerty
- abc123
- monkey
- 1234567
- letmein
- trustno1
- dragon
- baseball
- 111111
- iloveyou
- master
- sunshine
- bailey
- bailey
- passw0rd
- shadow
- 123123
- 654321
- superman
- qazwsx
- michael
- football
Print Friendly Single Article:25 Worst Passwords of 2011
Finland Citizens Urged to Change Online Passwords - 2011-11-14

The Finnish NBI (National Bureau of Investigation) is urging all Finns to change all passwords after a major leak this weekend. Over 100,000 email addresses and 15,000 passwords were leaked on Saturday. Officials fear more passwords will be leaked.
According to The Helsingin Sanomat, the Finnish computer publication MikroPC reports that some of the information has leaked from discussion forums operating on a phpBB2 platform.
This highlights an important consideration for users everywhere. Certain platforms are more "vulnerable" to hacking than others. Canned third party web platforms such as PHPBB, Wordpress, Joomla, Drupal, and many more are evolving daily. The teams working on these projects do a great job quickly patching vulnerabilities, but the websites running them must apply the patches on a regular basis, or they are left vulnerable.
Many small niche blogs and websites are run by by small staffs or individuals in their spare time. If one of these sites requires you to register with email and/or password, always use a junk email account and password for registration.
Print Friendly Single Article:Finland Citizens Urged to Change Online Passwords
Steam Breach - Lots of Personal Data, little worry of password compromise - 2011-11-11
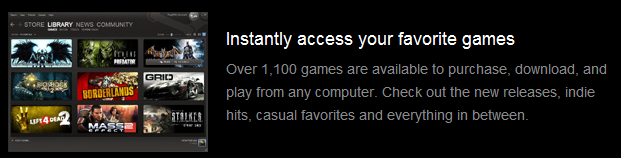
Steampowered.com, the website of over 1100 games has reported a breach:
The bad news is they are reporting an entire database compromise including user names, hashed and salted passwords, game purchases, email addresses, billing addresses and encrypted credit card information.
The good news is passwords were salted and encrypted, making it very difficult to obtain the password, and credit card data was encrypted.
The following announcement was sent to users
Dear Steam Users and Steam Forum Users, Our Steam forums were defaced on the evening of Sunday, November 6. We began investigating and found that the intrusion goes beyond the Steam forums. We learned that intruders obtained access to a Steam database in addition to the forums. This database contained information including user names, hashed and salted passwords, game purchases, email addresses, billing addresses and encrypted credit card information. We do not have evidence that encrypted credit card numbers or personally identifying information were taken by the intruders, or that the protection on credit card numbers or passwords was cracked. We are still investigating.
Sophos' recommendation to users is perfect, we're going to Copy and Paste it: ( Credit: Sophos report on Steam breach
Change your Steam password, just in case. If you were using a weak password before, take this opportunity to choose a decent one.
Keep an eye on your credit card statement and report any unexpected transactions.
Consider not storing your credit card data on Steam's servers. You don't have to. You can choose to enter it every time you need it instead.
Consider enabling Steam Guard. If you do, Steam will email you every time you (or someone else) logs in from someone else's computer.
Send an email to Steam asking why they encrypted credit card data and passwords, but apparently not the rest of its users' personally identifiable information.
If Steam truly did salt passwords, passwords changes may not be necessary. It's better to be safe than sorry.
Print Friendly Single Article:Steam Breach - Lots of Personal Data, little worry of password compromise
New Website May Find Your Insecure Password Before Most Hackers Do - 2011-11-04
 A new site, pwnedlist.com, now has spiders crawling the web looking for breached or vulnerable password lists. The site was created by Alen Puzic and Jasiel Spelman, two security researchers from DVLabs, a division of HP/TippingPoint.
A new site, pwnedlist.com, now has spiders crawling the web looking for breached or vulnerable password lists. The site was created by Alen Puzic and Jasiel Spelman, two security researchers from DVLabs, a division of HP/TippingPoint.
According to the site's "learn" page, the site does not keep any email data submitted through queries (no phishing). The little they reveal about site architecture is great. We are big fan of Amazon Simple DB (SDB) and feel it's the one the least vulnerable database platforms a website can use.
For the truly skeptical, the site enables users to submit their email as an SHA-512 hash See what are hashes and rainbow tables.
We tested a known bad email from a recent hack and it did not show up in the database. In fairnmess, the same address was not found in shouldichangemypassword.com either.
The sites domain was registered in June 2011 under a proxy service, which is very common and does not raise any flags. The founder is a well respected and active member of the security community. All timelines on personal and business twitter feeds correlate properly. We started this article on November 1st, and submitted some questions to the website. In the three days that followed we've received no response, but at least dozen publications have reported on pwnedlist.com, including Brian Krebs and Kaspersky Labs.
Every indication points to pwnedlist.com being a great resource.
Related Stories
Kaspersky Labs ThreatPost has the only real interview with founder, Alen Puzic as of 04-Nov-2011.
Brian Krebs has a good article geared toward the more technical crowd.
Print Friendly Single Article:New Website May Find Your Insecure Password Before Most Hackers Do
Lying about your Name or Age on the Internet May Get Difficult - 2011-11-01
 A new service promises to accurately verify your name and age. While this may not seem important for adults, for minors, this could be a huge advancement, although the site's terms requires persons to be 18 or older for verification. Update 1-Nov-2011 Tru.ly co-founder, David Gordon told us that a new API version will be implemented for parental verification to setup minor accounts.
A new service promises to accurately verify your name and age. While this may not seem important for adults, for minors, this could be a huge advancement, although the site's terms requires persons to be 18 or older for verification. Update 1-Nov-2011 Tru.ly co-founder, David Gordon told us that a new API version will be implemented for parental verification to setup minor accounts.
The site is currently in "beta", which means it's allowing public testing, but not quite ready for production.
Tru.ly uses "verification partners" to authenticate your identity. This is done by matching your submitted information with that in a national database of government and public data. In order to become verified, specific pieces of information must match. They report to use proprietary technology to flag users who may be trying to conduct fraud.
At this time the site asks for
Email Legal First Name Legal Last Name Last Four SSN digits Birthdate Permanent street addresss Permanent zip code
According to their website, Tru.ly's goal is to provide users with a single, verified identity on the internet. The service enables verified users to generate their own QR code  enabling users to provide an ID without divulging details. How this will be accomplished is not stated. Tru.ly also promises a browser plugin to see what profiles are verified on social networks. The plug in also has very limited details. Update 1-Nov-2011 We asked co-founder David Gordon about this, and he told us: "We didn't see much traction on it so we took it down and will plan on relaunching it with a larger audience."
enabling users to provide an ID without divulging details. How this will be accomplished is not stated. Tru.ly also promises a browser plugin to see what profiles are verified on social networks. The plug in also has very limited details. Update 1-Nov-2011 We asked co-founder David Gordon about this, and he told us: "We didn't see much traction on it so we took it down and will plan on relaunching it with a larger audience."
Should you trust tru.ly with your identity? We're not sure yet. We see no warning flags. No single piece of required information is highly sensitive alone, yet combined, they compromise more than many may wish to entrust to an internet company. 1-Nov-2011 Update We asked co-founder David Gordon about this and he said: "We use a high level SSL certification. user personal identifiable data is never stored on tru.ly servers. Third party accreditation is in process."
To our knowledge tru.ly is the first company to offer such a service. A March 2011 estimate by ComScore surmised that 3.6 million of Facebook’s 153 million monthly visitors in the United States are under 12. Facebook's terms of service require a minimum age of 14. A large component of tru.ly's offering is an API (Application Programming Interface), businesses can use to verify someone's identity. If Facebook, twitter, gambling, and adult content sites begin using the service, the internet may become a much safer place for kids.
One complication with kids is raised when reviewing the tru.ly terms of service. According to those terms, you must be at least 18 to be verified. This leaves a four year gap between the Facebook policy and the tru.ly policy.
Print Friendly Single Article:Lying about your Name or Age on the Internet May Get Difficult
Bloggtoppen.se 90000 Passwords Revealed - 2011-10-26
 Popular Swedish blogging site Bloggtoppen.se suffered a security breach compromising 90000 user passwords. The attackers allegedly publicly announced the password file details using a compromised Twitter account William Petzall, a former scandalized politician.
Popular Swedish blogging site Bloggtoppen.se suffered a security breach compromising 90000 user passwords. The attackers allegedly publicly announced the password file details using a compromised Twitter account William Petzall, a former scandalized politician.
The passwords were encrypted using an unsalted MD5 hash. (For more on hashes see See what are hashes and rainbow tables.) This means that users who had a strong password are less vulnerable than users using weak passwords. Strong passwords have mixed case, special characters, 10+ character length, no dictionary words. (See qualities of a strong password) According to analysis by dlitz.net, the most common password from the file was "super123".
#1 (995): super123 #2 (141): hejsan #3 (118): 123456 #4 (111): #5 (102): hejhej #6 (96) : bajskorv #7 (93) : sommar #8 (69) : hemligt #10 (60) : blomma #11 (54) : dinmamma #12 (52) : cocacola #13 (51) : stockholm #14 (50) : johanna #15 (45) : kalleanka #16 (44) : sverige #17 (43) : mammapappa #18 (43) : amanda #19 (43) : losenord #20 (43) : apelsin #21 (41) : qwerty #22 (41) : sommarlov #23 (40) : hundar #24 (39) : smulan #25 (38) : iloveyou #26 (38) : lösenord #27 (38) : password #28 (37) : abc123 #29 (35) : internet #30 (35) : fotboll **Analysis credit: https://www.dlitz.net/blog/2011/10/most-common-losenord/
According to a notice at the site:
Blog Top is closed until further notice due to system maintenance alleged hacking. Unknown perpetrators have come across the user database with user names, email addresses and hashed passwords, which means that if you, the user has used the same login information for other services on the web so likely these accounts to be hijacked. We recommend all users to immediately change passwords on all accounts use the same login information here. Further information will come when we have had time to investigate and resolve the interference.
If you ever had an account at Bloggtoppen.se, and reuse passwords at multiple sites, start changing passwords. Always start with your email password and work back from there. Follow Healthy Password rules when creating your new passwords.
Print Friendly Single Article:Bloggtoppen.se 90000 Passwords Revealed
Order and Chaos Online Hacked - 2011-10-20

According to TouchArcade.com, online gaming site, Order and Chaos, has been hacked.
Users of all versions, including facebook and mobile, are reporting compromised accounts.
If you have ever used this site, or the Gameloft live service, and share passwords, change your passwords. Start with email and work back from there. As always, remember to follow healthy password rules
Print Friendly Single Article:Order and Chaos Online Hacked
iPhone 4s Siri Bypasses Password Security - 2011-10-20

Graham Cluley of Sophos exposed a new iPhone vulnerability in a blog post yesterday.
The vulnerability is with the new voice assistant Siri. Siri will respond to any stranger while the phone is locked and bypasses some password security.
Strangers can Compose and send email, compose and send text messages, and change calendar entries.
Fixing the problem is easy by navigating to "Settings/General/Passcode Lock" and changing the Siri setting to OFF.

Print Friendly Single Article:iPhone 4s Siri Bypasses Password Security
A New Way to Steal Smart Phone Passwords - 2011-10-18
 Researchers from Georgia Tech have found a way to triangulate your passwords by using your smart phone's accelerometer. The accelerometer is a sensor that enables your phone's screen to re-orient itself when you turn the phone. According to an article in MIT Technology Review, it is possible for malware to determine your password with 80% accuracy when the password is entered with the device laying on a flat surface.
Researchers from Georgia Tech have found a way to triangulate your passwords by using your smart phone's accelerometer. The accelerometer is a sensor that enables your phone's screen to re-orient itself when you turn the phone. According to an article in MIT Technology Review, it is possible for malware to determine your password with 80% accuracy when the password is entered with the device laying on a flat surface.
You don't need to worry yet, but in the near future, it may be "smart" to only enter passwords into your smart phone while holding it in your not-so-steady hands.
Print Friendly Single Article:A New Way to Steal Smart Phone Passwords
Fake Android Netflix App Steals Credentials - 2011-10-13
 A new credential stealing fake Android Netflix app is floating around. The app looks nearly identical to the real one. Instead of taking you to content, the app will just ask you to authenticate.
A new credential stealing fake Android Netflix app is floating around. The app looks nearly identical to the real one. Instead of taking you to content, the app will just ask you to authenticate.
If you've recently installed the netflix android app and failed to see your content, get to netflix right away an change your credentials. Also change passwords at any other sites sharing that password. Always start with your email and work down from there.
 Credit: Symantec.com
Credit: Symantec.com
Netflix customers that are looking for a legitimate Android Application developed by Netflix, Inc. can find it on the official Android Market. Downloading from trusted sources is part of practicing good security for your mobile device.
Print Friendly Single Article:Fake Android Netflix App Steals Credentials
BlueHomes.com breached over 150,000 plain text passwords exposed - 2011-10-12
 Over 150,000 plain text passwords and usernames were breached from popular European properties site, bluehomes.com. The hacker posted a link to the dump on pastebin yesterday. The hacker claims the dump contains more than 500,000 passwords, but our best estimate is more like 150,000
Over 150,000 plain text passwords and usernames were breached from popular European properties site, bluehomes.com. The hacker posted a link to the dump on pastebin yesterday. The hacker claims the dump contains more than 500,000 passwords, but our best estimate is more like 150,000
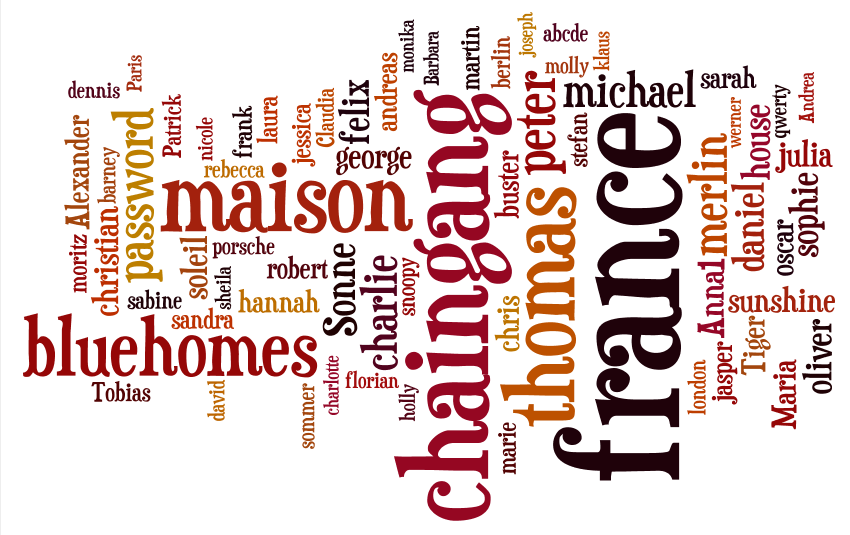 *Wordcloud credit wordle.net
*Wordcloud credit wordle.net
*Note: pure numeric passwords were omitted.
In addition to usernames and passwords, the dump also includes over 80 megabytes of sensitive customer, employee data, and infrastructure data.
Print Friendly Single Article:BlueHomes.com breached over 150,000 plain text passwords exposed
Patch Tuesday Again - 2011-10-12
Windows users need to remember to check that windows last night or sometime in the next day or two. This patch Tuesday Apple released an iTunes patch for Windows. To get the iTunes patch, run iTunes.
The best reference for seeing what's included in patch Tuesday is Krebsonsecurity.com
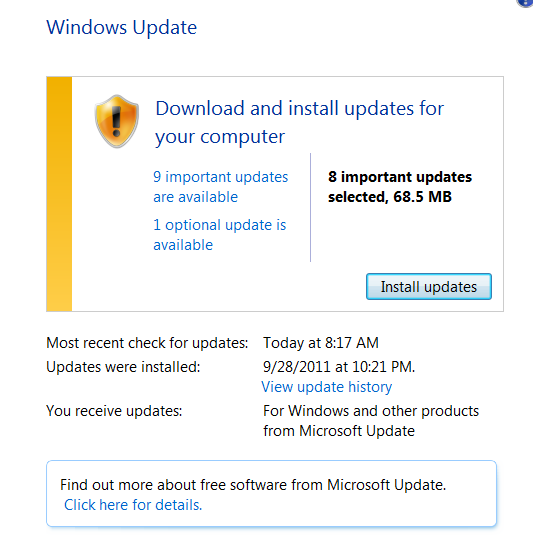
Corporate users may not see update notifications. For more on how to update your Windows system, see http://www.healthypasswords.com/content.How_to_Check_Windows_Update.html .
Print Friendly Single Article:Patch Tuesday Again
WineHQ breach exposes contributor usernames and passwords - 2011-10-12
 WineHQ is a website supporting Wine. Wine lets user run Windows software on other operating systems. With Wine, users can install and run these applications just like they would in Windows.
WineHQ is a website supporting Wine. Wine lets user run Windows software on other operating systems. With Wine, users can install and run these applications just like they would in Windows.
According to thinq.co.uk, "This means that they have all of those emails, as well as the passwords," Jeremy White of project organiser CodeWeavers confirms in his mailing list post. "The passwords are stored encrypted, but with enough effort and depending on the quality of the password, they can be cracked.
This breach will impact a narrow band of technical users, who hopefully know better than to share usernames and passwords between sites.
Print Friendly Single Article:WineHQ breach exposes contributor usernames and passwords
Sony breach impacts 93000 users - 2011-10-12
 Sometime between October 7 and October 10, The Sony Playstation Network detected a high volume of unauthorized logins. Sony locked about 93,000 accounts whose IDs and passwords were successfully breached.
Sometime between October 7 and October 10, The Sony Playstation Network detected a high volume of unauthorized logins. Sony locked about 93,000 accounts whose IDs and passwords were successfully breached.
Sony sent email notifications and password reset procedures to breached account holders. Sony reports that no credit card data was taken
If you have been notified by Sony, or hold a playstation network account, change your password and any other site passwords sharing the same user/password. Always start by changing with your email. Email is always the first target after any breach.
Update 2011-10-12 16:30 GMT
According to recent reports, the usernames and passwords used against the Sony network were not obtained from Sony, but from another source.
In an April breach, Sony was criticized for taking weeks to notify users. In this case, Sony may have notified users with too little information. Sony appears to be a target and not a source. Playstation users should still take precautions and change passwords. Hopefully Sony will provide the email addresses to security experts, who can bounce the attempted logins against known breach lists to determine the source.
References
Print Friendly Single Article:Sony breach impacts 93000 users
Only 38% of account holders know how their account was compromised - 2011-10-07

According to recent research by commtouch, a leading messaging and Web security technology company, few account holders ever find out how their account was compromised. A more alarming 23% of compromised account holders did nothing to remedy the problem.
How was your account compromised?
62% - Not sure
15% - Clicked Facebook Link
15% - Public WiFi
4% - Clicked on an Email Virus
Only one in eight compromised email accounts resulted in the classic "I'm stuck in a foreign country please send money" message to friends.
What was done with your Hacked account?
54% - Send Spam
23% - Not Sure
12% - Scams
8% - Phony facebook post
How did you hear your account was hacked?
54% - Friends told me
31% - Noticed Myself
15% - Official Email from Provider
How did you fix your hacked account?
65% - Changed Password
31% - Ran Anti-Virus
23% - Did Nothing
Print Friendly Single Article:Only 38% of account holders know how their account was compromised
Unijobs.com.au hack exposes over 600 passwords - 2011-10-07
 The popular Australian university job website, UniJobs.com.au was hacked.
The popular Australian university job website, UniJobs.com.au was hacked.
The usernames (email addresses) and hashed passwords ( what are password hashes)are posted on pastebin at http://pastebin.com/Nrd8MaKD yesterday.
The post included MD5 hashes and plain text password for cracked passwords. Most of the passwords in the list appeared to be the initial system generated passwords. They were mostly six digit passwords using mixed case letters and numbers. There were several dozen real passwords in the list. These are the people who are probably vulnerable to other compromised accounts.
The post only showed 629 of the 780 cracked, but that appears to be where the cracking was at when the post occurred. Most likely the rest of the list has been cracked by now.
Because these posts quickly disappear from pastebin, we have posted just the email addresses here .
Print Friendly Single Article:Unijobs.com.au hack exposes over 600 passwords
Associated Press-MTV poll finds 3 in 10 teens and young adults impersonated online - 2011-10-06
According to the Associated Press, a new Associated Press / MTV poll found that 3 of 10 teens reported being impersonated or monitored online.

In the AP-MTV poll, two-thirds of those who had been hacked said at some point they've changed their password in response to digital abuse. 46 percent have altered their email address, screen name or phone number, and 25 percent have deleted a social networking profile.
The poll cites several cases where roommates or friends impersonated each other as pranks. In two cited cases, the incidents were considered harmless and fun. In other cited cases, the intent appears cruel.
In our opinion the 3 in 10 number may not translate the same for adults. Adults don't typically room together in dorms, or hang out in friends bedrooms where access to open browser sessions or saved logins are as easy. For most adults, the biggest equivalent risk is leaving a laptop open or an unlocked desktop at work. The lesson everyone should take away from this poll is to not save logins for convenience and follow healthy password practices.
Print Friendly Single Article:Associated Press-MTV poll finds 3 in 10 teens and young adults impersonated online
Why Would Anyone Want My Password? - 2011-10-05
We talk to a lot of different people about passwords every day. Most users always say, "Who would want my password?". We then explain how most people share passwords and a compromised email can compromise other more important accounts. Sadly, most people don't get it until it happens to them.
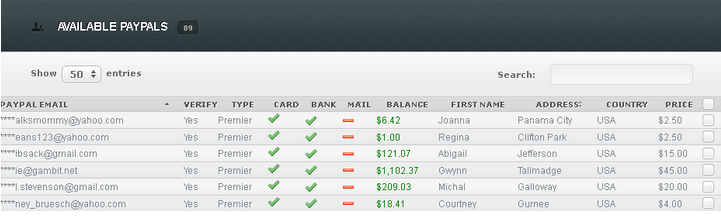
Image Credit: Krebsonsecurity.com
This recent report from Brian Krebs shows how your compromised information get's sold. These types of online market places exist for every type of credential: Credit Cards, Online Payments, Email Accounts, Social Networking accounts, and more.
Don't wait until it's too late. Create a password strategy, review and adjust it twice a year.
Print Friendly Single Article:Why Would Anyone Want My Password?


|
Don't become a news story... |

|
| ISBN: 978-0615456850 |
Knowledge is the best home security. |
.
|
|
||
|
Home | Live CD Listing | Password Worksheet | Third Party Ratings | Purchase | Errata | Contact | News | News Archive | Legal Copyright © 2011, Sustainable Alternatives, LLC | Ligonier, PA 15658 | 724-238-9560 | All Rights Reserved. |

|
|
 |
.

